"Threat Actor Turns Thousands of IoT Devices Into Residential Proxies"
Share
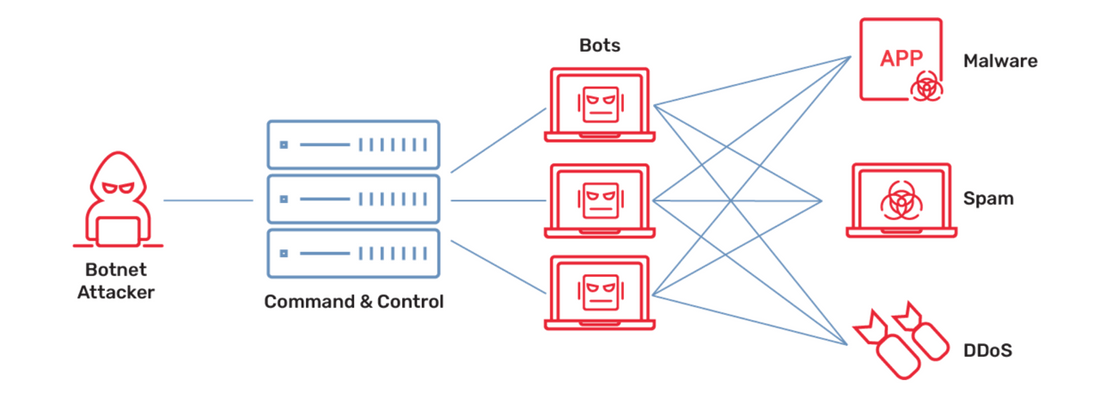
According to security researchers at Trend Micro, a threat actor is monetizing vulnerable Internet-of-Things (IoT) devices by infecting them with malware and listing them as residential proxies within minutes after exploitation. The threat actor is tracked as Water Barghest and has compromised over 20,000 IoT devices to date, renting them to threat actors looking to anonymize their activities. Active for at least five years, Water Barghest has remained under the radar by extensively relying on automation, erasing log files to cover its tracks, and only accepting cryptocurrency payments. The researchers noted that the threat actor acquires IoT device vulnerabilities (including zero-days), uses publicly available online scanners to identify vulnerable devices, and then attempts to exploit them from a set of data center IP addresses. Compromised devices are quickly monetized on specialized marketplaces. As of October 2024, the threat actor had created a botnet of over 20,000 devices from Cisco, DrayTek, Fritz!Box, Linksys, Netgear, Synology, Tenda, Western Digital, and Zyxel, all of which were infected with the Ngioweb malware. Initially observed in 2018, when it was targeting Windows systems, Ngioweb started targeting Linux computers in 2019 and switched focus to IoT devices in 2020. A new variant of Ngioweb was seen this year. The researchers said that the demand for these botnets will likely increase because both APTs and financially motivated groups will continue using third-party IoT botnets and commercially available residential proxy services for anonymization and espionage.
SecurityWeek reports: "Threat Actor Turns Thousands of IoT Devices Into Residential Proxies"
